AI Detection and Response
See and Stop Agent Risk at Runtime
Intent-aware detection and response with full visibility into execution paths, decisions, and actions across agentic platforms.
Recognized by




































Runtime Agent Risk Is Easy to Miss
AI agents operate autonomously, executing actions across systems, tools, and workflows. At runtime, risk emerges through decision paths, tool invocations, memory updates, and chained actions often without a single malicious prompt or obvious signal.
Most security tools were not designed to observe or govern this execution layer. Controls focused on prompts, outputs, or isolated events miss how agents behave over time and how intent materializes across actions.
Zenity’s AI Detection & Response (AIDR) capabilities are purpose-built to monitor agent intent and execution paths at runtime. By observing how agents reason, act, and chain decisions in real environments, AIDR enables security teams to detect and stop risky behavior before it impacts systems or data.

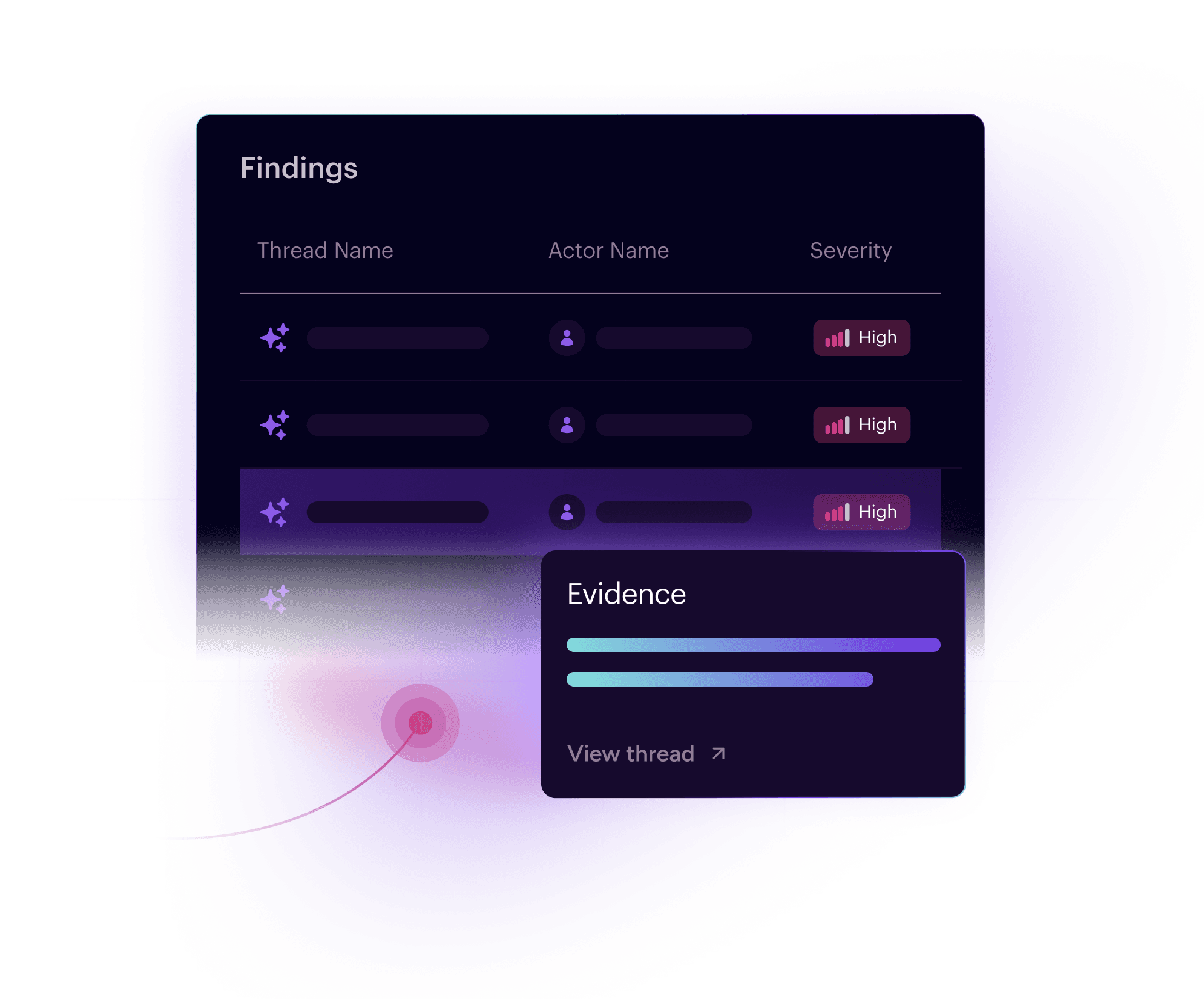
Detect What Agents Actually Do
AIDR analyzes agent intent, execution paths, and behavior not just individual events. By understanding what an agent is trying to do and how actions unfold over time, AIDR surfaces runtime risk that prompt filtering and event-based detection cannot see.
Intent-Based Detection
Analyze full agent execution context including tool calls, memory access, data access & usage, and control flow to identify malicious behavior.
Complete Agent Context
Correlate buildtime risk with runtime execution using shared intelligence from AI Observability and AISPM.
Automated Response at Agent Speed
Contain risk in real time with agent quarantine, permission revocation, execution blocking, and automated remediation.
Detection & Response Built for Agent Behavior

Real-Time Protection for Modern Agent Deployments
AIDR protects AI agents at the moment risk materializes. Whether agents are embedded in SaaS platforms or custom-built for business workflows, AIDR enables security teams to detect and stop unsafe behavior as it unfolds, without interrupting legitimate operations.
Prompt Injection
AIDR detects direct and indirect prompt injection that causes agents to execute unsafe actions, alter control flow, or invoke unintended tools and blocks execution before impact
Data Exfiltration
Real-time monitoring and blocking of sensitive data leakage through agent conversations, tool calls, and memory persistence
Privilege Escalation
Continuous monitoring for unauthorized permission increases and lateral movement between agents and systems
Multi-Agent Attacks
Advanced threat detection across complex agent workflows to identify coordinated attacks and sophisticated threat patterns
Memory Poisoning
Real-time detection and prevention of malicious context injection and agent memory manipulation attacks
Tool Misuse
Automated blocking of unauthorized tool invocations and API calls that violate security policies or business rules
Trusted by Forward-Looking Security Leaders
“With Zenity we were able to build a program to remediate existing vulnerabilities with a product that relies on self service and auto-fix so we can scale.”
Existing vulnerabilities remediated within 4 months with 2 FTEs
Tenant grew over 12 months
“We needed a way to partner with the business. Zenity gives us confidence to continue enabling our employees to innovate with AI Agents and applications.”
People developing these systems are not professional developers
Instances of agents and apps that were shared across the entire org
"Zenity provided a preventative layer to proactively reduce security violations of our Agentic AI use. As a result, we saw tremendous growth in cross-departmental adoption of AI Agents."
Reduction in security violations
High-risk violations automatically remediated
"With Zenity, we identified and managed risks from a huge attack surface containing over-shared resources that had access to sensitive data, DLP bypass routes, and misconfigured AI Agents."
Risk reduction across the tenant containing 150k+ total resources
Growth in agent, app, and automation volume
“With Zenity we were able to build a program to remediate existing vulnerabilities with a product that relies on self service and auto-fix so we can scale.”
Existing vulnerabilities remediated within 4 months with 2 FTEs
Tenant grew over 12 months
“We needed a way to partner with the business. Zenity gives us confidence to continue enabling our employees to innovate with AI Agents and applications.”
People developing these systems are not professional developers
Instances of agents and apps that were shared across the entire org
"Zenity provided a preventative layer to proactively reduce security violations of our Agentic AI use. As a result, we saw tremendous growth in cross-departmental adoption of AI Agents."
Reduction in security violations
High-risk violations automatically remediated
"With Zenity, we identified and managed risks from a huge attack surface containing over-shared resources that had access to sensitive data, DLP bypass routes, and misconfigured AI Agents."
Risk reduction across the tenant containing 150k+ total resources
Growth in agent, app, and automation volume
“With Zenity we were able to build a program to remediate existing vulnerabilities with a product that relies on self service and auto-fix so we can scale.”
Existing vulnerabilities remediated within 4 months with 2 FTEs
Tenant grew over 12 months
“We needed a way to partner with the business. Zenity gives us confidence to continue enabling our employees to innovate with AI Agents and applications.”
People developing these systems are not professional developers
Instances of agents and apps that were shared across the entire org
"Zenity provided a preventative layer to proactively reduce security violations of our Agentic AI use. As a result, we saw tremendous growth in cross-departmental adoption of AI Agents."
Reduction in security violations
High-risk violations automatically remediated
"With Zenity, we identified and managed risks from a huge attack surface containing over-shared resources that had access to sensitive data, DLP bypass routes, and misconfigured AI Agents."
Risk reduction across the tenant containing 150k+ total resources
Growth in agent, app, and automation volume
Analyst Recognition & Research Coverage
Start Securing Your
AI Agents Today
Your AI is already live. Is your security catching up?Zenity brings observability, enforcement, and protection under one roof.
Get a Demo